Category: web
02/23/06 10:33 - 30ºF - ID#21548
Disabling the nasty clipboard reader
1. Under the Tools menu, select Internet Options
2. Click on the Security tab.
3. In the box labelled, "Security level for this zone", click on Custom Level
4. Scroll all the way down to the Scripting heading
5. Under "Allow paste operations via script" choose the Disable button.
6. Click OK and confirm that Yes you do want to change security settings for this zone.
Permalink: Disabling_the_nasty_clipboard_reader.html
Words: 119
Category: security
02/17/06 03:05 - 26ºF - ID#21547
Windows IE security issue with clipboard
 I created. The data will be alerted and although I am not collecting the data anyone could use this technology to steal and forward whatever information was in your clipboard when you visited their web page. Just think about what you copy into your clipboard when using IE, your passwords, your bank account info, etc. Get firefox
I created. The data will be alerted and although I am not collecting the data anyone could use this technology to steal and forward whatever information was in your clipboard when you visited their web page. Just think about what you copy into your clipboard when using IE, your passwords, your bank account info, etc. Get firefox 
--paul
Permalink: Windows_IE_security_issue_with_clipboard.html
Words: 96
Category: browsers
02/16/06 05:47 - 40ºF - ID#21546
Camino 1.0 released
Camino 1.0 brings you a heavily-updated version of the only native Mac OS X browser using Mozilla's Gecko rendering engine. Thousands of bugs were fixed in Gecko 1.8, providing users with improved web page compatibility.
more info:

Permalink: Camino_1_0_released.html
Words: 41
Category: web
01/31/06 03:05 - 33ºF - ID#21545
Microsoft Developer Toolbar
 like the one firefox has. It could have saved me thousands of hours had they realeased this before but at least it is a step iun the right direction.
like the one firefox has. It could have saved me thousands of hours had they realeased this before but at least it is a step iun the right direction.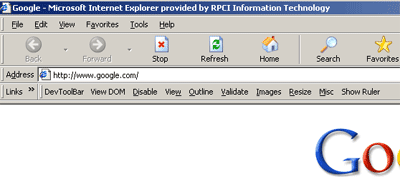
Permalink: Microsoft_Developer_Toolbar.html
Words: 60
01/31/06 12:05 - 39ºF - ID#21544
face the nation
Does anyone else get nostalgic for "vintage" [inlink]twisted,296[/inlink] computer memorabilia? I wish I had screenshots of some of my old desktops.
Permalink: face_the_nation.html
Words: 25
Category: privacy
01/30/06 09:47 - 39ºF - ID#21543
Internet Privacy
I think that for the vast majority of internet users, privacy is just an illusion. Even if you use a firewall, http (Hyper Text Transfer Protocol) sends all sorts of data about you, your computer, your browser and even your monitor's screen resolution to the websites that you surf.
Your IP
When you surf the internet, your connection is uniquely identified by an IP (internel Protocol) number. If you are on a LAN (Local Area Network) you may share that IP with others on the same network.
In general terms for people who surf the 'net at home, knowing a user's IP is enough to find him or her. But . . .
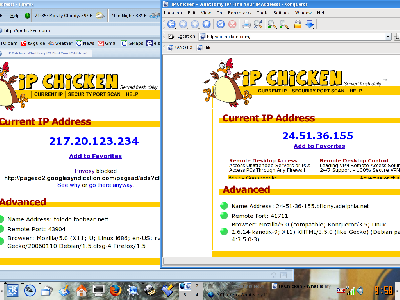
The above is a screenshot with firefox on the left running tor (more about that later in this journal) and konqueror on the right. Both browsers show the ipchicken website
 which shows my old Linux box's IP. Notice that two different IPs are being returned at the same time.
which shows my old Linux box's IP. Notice that two different IPs are being returned at the same time.Privacy at an Internet Cafe?
That's why some people go to internet cafes to surf the 'net. But even that can be problematic since the IP can be traced back to the cafe and computers can be forensically examined - most computers retain much data related to surfing the net - cookies, cached data, etc.
And that is why some people get online at internet cafes using "live cd" operating systems that boot and run entirely from the cd without writing any data to the hard drive. Some good Linux live cds that I have used are SimplyMepis
 Knoppix
Knoppix  Kanotix
Kanotix  PCLinuxOS
PCLinuxOS  Ubuntu
Ubuntu  and Slax
and Slax 
But that still does not solve the IP problem. There are also several live cds that are designed for getting online anonymously and privately including Anonym.OS (an OpenBSD distrobution)
 and Phantomix
and Phantomix 
Tor - privacy at home?
The Electronic Frontier Foundation
 recommends the use of Tor
recommends the use of Tor 
Your traffic is safer when you use Tor, because communications are bounced around a distributed network of servers, called onion routers. Tor's technology aims to provide Internet users with protection against "traffic analysis," a form of network surveillance that threatens personal anonymity and privacy, confidential business activities and relationships, and state security.
I installed and set up tor and firefox on my old Linux box this evening, and it seems to work as promised. Given the nature of how tor works browsing even on a broadband connection is slower.
Permalink: Internet_Privacy.html
Words: 447
Category: vnc
01/19/06 08:18 - 38ºF - ID#21542
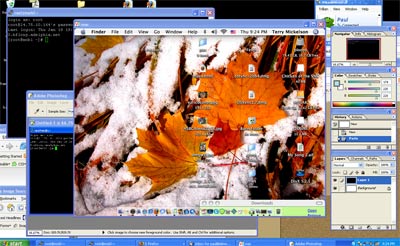
tunneling VNC through putty
Here you can see my mac desktop on my windows desktop
You can download a VNC server and client here
 or at the original hoem of realVNC
or at the original hoem of realVNC 
Unfortunately, it is not the most secure thing out there. Yes, ytou can buy expensive versions that are highly encrypted but the easiest thing to do, is to tunnel your VNC connection through an SSH client such as putty.
This for example lets me visually control my linux server from afar. In a home network this would allow you to use one computer from a window on another to say change msuci on the computer downstairs.
So anyways if you are using VNC client on windows to view you other desktop, it is easy and freee to pipe it over putty.
Here is how you would do it
 I copied the info here to so that in case that link goes down you can still find it here.
I copied the info here to so that in case that link goes down you can still find it here.If the VNC Server is running on a Linux machine or it is running on a Windows machine that is also running sshd, then setup a tunnel from client machine to server machine with: (The following instructions are for PuTTY
 , adjust accordingly.)
, adjust accordingly.)* After entering the address of the client machine, go to the "Tunnels" section under SSH.
* Enter 5901 in the "Source port" box under the "Add new forwarded port" section.
* Enter "localhost:5901" in the "Destination" box
* Make sure that the "Local" radio button is selected
* Click the "Add" button and the information should appear in the "Forwarded ports:" box.
* One can now initiate the connection by pressing the "Open" button
* Once the connection is established, the VNC client can be started from the Windows menu (use display 1)
Permalink: tunneling_VNC_through_putty.html
Words: 391
Category: windows
12/30/05 12:39 - 28ºF - ID#21541
Windows Security Flaw is "Severe"
Source:Unlike with previously revealed vulnerabilities, computers can be infected simply by visiting one of the Web sites or viewing an infected image in an e-mail through the preview pane in older versions of Microsoft Outlook, even if users did not click on anything or open any files. Operating system versions ranging from the current Windows XP to Windows 98 are affected.

This flaw exploits the Windows Graphics Rendering Engine and is reported to affect Internet Explorer, Outlook, and Outlook Express, as well as Firefox and Opera.
editorial aside: Since it is has suggested by an e-peep or two that the "Lib" media can not be trusted, I'm certain that all you Windows users have nothing to worry about since the Washington Post is reporting this. ;-)
Another source of information about this flaw is that purveyor of "Trustworthy Computing" -- Microsoft.

Based on our investigation, this exploit code could allow an attacker to execute arbitrary code on the user's system by hosting a specially crafted Windows Metafile (WMF) image on a malicious Web site. Microsoft is aware that this vulnerability is being actively exploited.
Microsoft has determined that an attacker using this exploit would have no way to force users to visit a malicious Web site. Instead, an attacker would have to persuade them to visit the Web site, typically by getting them to click a link that takes them to the attacker's Web site. In an e-mail based attack, customers would have to be persuaded to click on a link within a malicious e-mail or open an attachment that exploited the vulnerability. In both the web and email based attacks, the code would execute in the security context of the logged-on user.
A possible workaround has been reported
 a word of warning: improperly changing the .dll settings of a computer can cause serious problems.
a word of warning: improperly changing the .dll settings of a computer can cause serious problems.
* Click on Start > Run.
* Type:
regsvr32 /u shimgvw.dll
* Click OK
* Click OK again when the dialog appears.
Note that this can have an effect on the display of some thumbnails in Windows.
Addendum: to reregister (undo the workaround) the .dll use this command: regsvr32 shimgvw.dll
Permalink: Windows_Security_Flaw_is_quot_Severe_quot_.html
Words: 386
Category: worms
12/22/05 11:59 - 26ºF - ID#21540
Santa IM worm hits AOL, MSN and Yahoo
A Santa Claus worm is attempting to trick America Online, Microsoft MSN and Yahoo instant-messaging users into clicking on a file that delivers unwanted software to a victim's computer.
The IM.GiftCom.All worm attempts to dupe IM users into thinking an acquaintance has sent them a link to a harmless Santa Claus file, according to a security advisory issued Tuesday by IMlogic.
People who click on the file will see an image of Santa, but what they are less likely to notice is a so-called rootkit being installed onto their system. A rootkit is a tool designed to go undetected by the security software used to lock down control of a computer after an initial hack. The malicious attacker can then distribute messages to the user's IM contacts, using a similar technique to lure the unsuspecting acquaintance to click on the link.

Permalink: Santa_IM_worm_hits_AOL_MSN_and_Yahoo.html
Words: 157
Category: usb
12/10/05 10:12 - 25ºF - ID#21539
Weird USB drives (Sushi anyone?)

On the other hand for the (e:peeps) in touch with their feminine side (no not you (e:jason)), there is always . . .

If you find this interesting, check out the rest of the top 10 weirdest USB drives at

--walt
Permalink: Weird_USB_drives_Sushi_anyone_.html
Words: 68
Author Info
Category Cloud
More Entries
After This
My Fav Posts
- This user has zero favorite blogs selected ;(

 mobile
mobile

